What is MEV?
MEV (maximum-extractable value) is a measure of the total amount of value that a miner, validator, sequencer, or other privileged protocol actor can make by arbitrarily including, excluding, or reordering transactions from the blocks they produce.
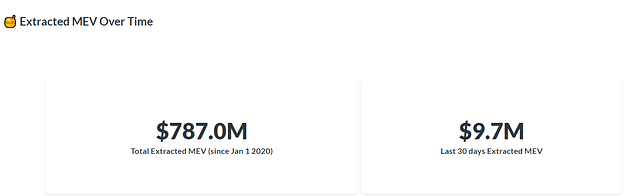
Data from https://explore.flashbots.net/ shows the total extracted MEV in Ethereum blockchain which is already $787M since Jan 1, 2020 with the majority of MEV came from AMMs (e.g. Uniswap, Sushiswap).
What is MEV’s impact on Index Coop’s DPI product?
IndexCoop’s (IC) largest AUM is DPI with a monthly rebalance schedule. IC rebalances DPI token by using AMM’s (Uniswap, Sushiswap, etc.) that are prone to sandwich attacks (type of MEV) especially with huge trade volume.
Sandwich attacks are composed of 3 transactions:
(Let us use WETH and Sushi token as an example)
-
Front-runner’s transaction - a bot will swap WETH for SUSHI, causing the price of SUSHI to go up
-
User’s transaction - user will swap WETH for SUSHI at a higher price
-
Back-runner’s transaction - a bot will swap SUSHI with a higher price for WETH, resulting in more WETH
Watch the video below to understand Sandwich Attacks: DeFi exploits: the sandwich attack - YouTube
What are the sandwich attacks that happened in DPI?
I used the tool https://sandwiched.wtf to check for sandwich attacks in DPI.
For more details visit: Sandwiched.wtf?
-
DPI suffered around 25 ETH (~50k USD in today’s ETH price) loss due to these sandwich attacks despite having a very tight slippage during the rebalancing period.
-
Tokens that had been sandwiched are LRC, YFI, CREAM, REN, COMP, UNI, SUSHI, and SNX.
-
Since launch, there were a total of 149 swaps made to rebalance the tokens mentioned above. Refer to link Dune Analytics.
-
29 out of 149 have been sandwich attacked. 16 out of these 29 attacks happened in Sushiswap while 13 happened in Uniswap.
-
Sandwich attacks started last April with 20 sandwich attacks: 0 for May, 6 for June, and 2 for July.
-
All of the attacks happened when swapping WETH to DPI’s underlying token (e.g WETH to YFI).
Proposed solutions:
Engineering team had performed an amazing job of minimizing MEVs. The 25 ETH loss is a small amount relative to the volume that they rebalanced. However, these losses will accumulate over time if we do not act on this problem (bigger losses in terms of USD if the ETH price goes above ATH).
- Use FlashDEX (ArcherSwap, MistX)
- Use CowSwap (Coincidence of Wants)
- Use Flashbots bundle
- Use UniswapV3 - with deeper liquidity, I think it is possible to adjust the swap with a tighter slippage.
Comparison between normal and flashbots transactions fees
I extracted the actual sandwich attack transactions Sandwiched.wtf and check the gas prices.
Based on this chart, the attackers are willing to pay an enormous price of gas as long as they have a net gain
This chart shows the average cost of transactions per day.
Uniswap is the cheapest, followed by MistX and ArcherSwap.
Note: I have already discussed this with Engineering Team, using FlashDEX or Flashbots will require huge engineering work, meaning this cannot be implemented soon. I will keep an eye on these attacks as well as analyzing other IC products for MEVs
Useful Articles